Last week, Guardian ran a story claiming that a backdoor built into WhatsApp can allows its parent company, Facebook, to read user messages despite advertising end-to-end encryption and complete privacy:
Facebook claims that no one can intercept WhatsApp messages, not even the company and its staff, ensuring privacy for its billion-plus users. But new research shows that the company could in fact read messages due to the way WhatsApp has implemented its end-to-end encryption protocol.
Open Whisper Systems, the nonprofit behind Signal protocol that powers WhatsApp’s end-to-end message encryption, came to WhatsApp’s defense and fired back at the Guardian story:
Today, the Guardian published a story falsely claiming that WhatsApp’s end to end encryption contains a “backdoor.” … The way this story has been reported has been disappointing. There are many quotes in the article, but it seems that the Guardian put very little effort into verifying the original technical claims they’ve made.
So what really happened? Tobias Boelter, who “discovered the vulnerability”, followed up to further explain and support the backdoor/vulnerability theory and why it matters:
… [WhatsApp] encrypted messaging works using secret and public keys. Every user has both a secret key known only to them, and a public key.
A user’s public key can be used to encrypt messages which can then only be made readable again with the associated secret key.
Okay, so public key encrypts and private key decrypts. Public key is publicly available to anyone, while private key stays private. Let’s continue.
A difficult problem in secure communication is getting your friend’s public keys. Apps such as WhatsApp and Signal make the process of getting those [public] keys easy for you by storing them on their central servers and allowing your app to download the public keys of your contacts automatically.
The problem here is that the WhatsApp server could potentially lie about the public keys. Instead of giving you your friend’s key, it could give you a public key belonging to a third party, such as the government.
So a third party, impersonating your friend, can give you its own public key and WhatsApp will overwrite your friends actual key with it thinking that it has changed. You will encrypt messages using the wrong key which allows the third party to read your messages. The third party can act as the man in the middle between you and your friend if it can compromise both, eavesdropping on the conversation while staying under your radar. But, in order to do any of this, it will require Facebook’s support and access to WhatsApp server infrastructure.
In reality, a user’s keys can change for any number of reasons. Wipe your device and reinstall the app or get a new device and you’ll get a new key. Open Whisper blog posts suggest that the way WhatsApp handles key change is appropriate:
The only question it might be reasonable to ask is whether these safety number [keys] change notifications should be “blocking” or “non-blocking.” In other words, when a contact’s key changes, should WhatsApp require the user to manually verify the new key before continuing, or should WhatsApp display an advisory notification and continue without blocking the user.
[…] we feel that their choice to display a non-blocking notification is appropriate. It provides transparent and cryptographically guaranteed confidence in the privacy of a user’s communication, along with a simple user experience.
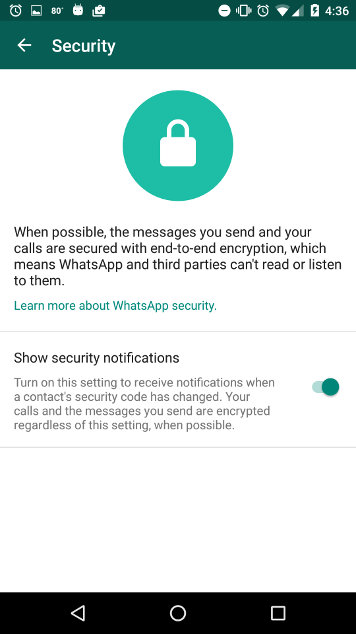
What the Open Whisper blog post doesn’t mention is that the “advisory notifications” are optional and not shown by default. Users need to turn the “Show security notifications” option on explicitly in order to receive notifications that their friend’s key has changed.
WhatsApp has done the right thing considering its market and users. Most of WhatsApp’s users can’t be bothered to verify security codes, much less understand what they mean. End to end encryption was introduced after WhatsApp was already very successful and had very large number of users. I doubt “blocking” or even “non-blocking” key change notifications that could potentially confuse users was even an option. They had to find the right balance between security and usability. WhatsApp is secure enough. But it does have a weakness and it’s plausible that if the Big Brother wants to tap into your WhatsApp messages or phone calls, it totally can… probably without you ever knowing.